Architecture, Implementation, and Security of the Super Agent Harness
1. Project Overview and Evolution
Definition and Core Identity
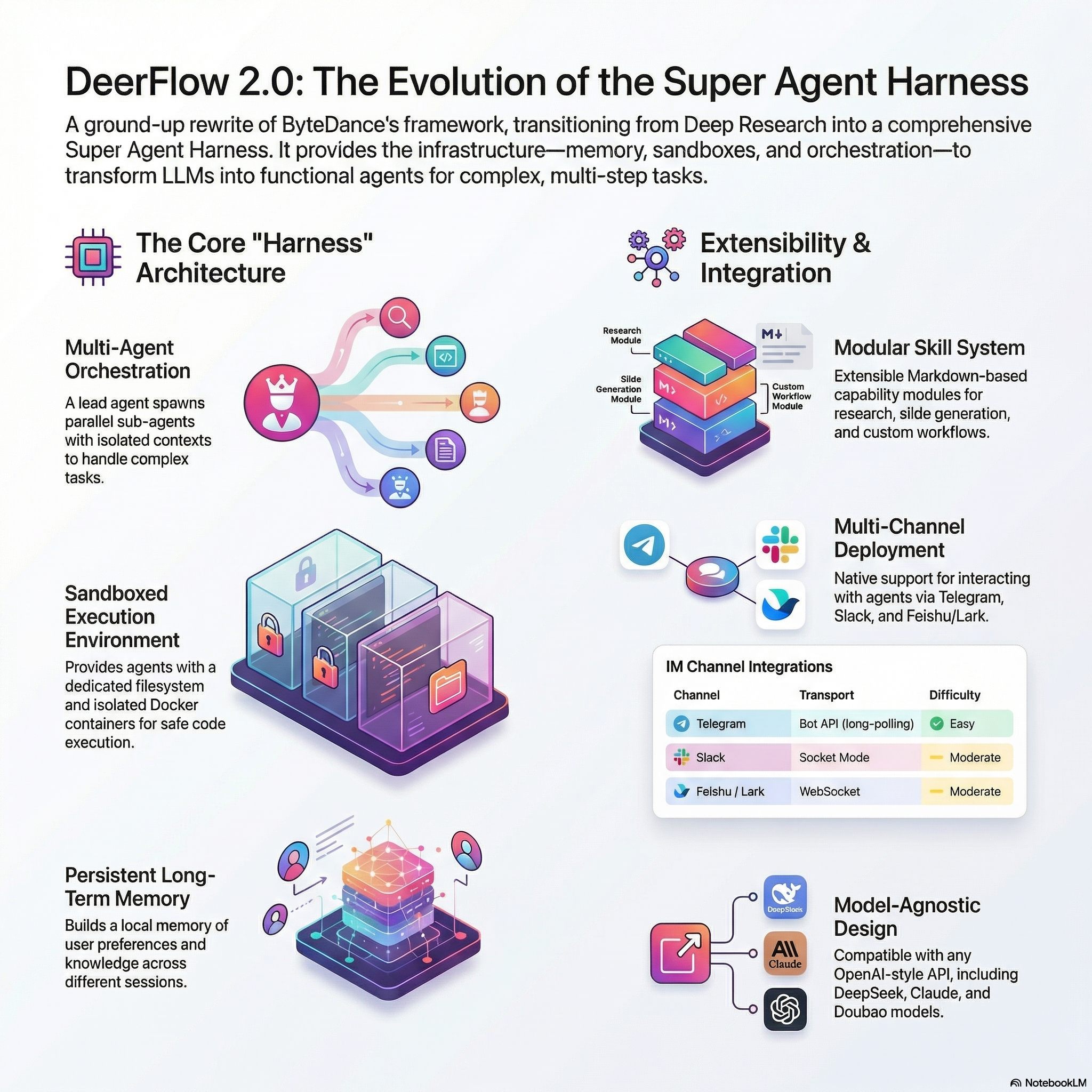
DeerFlow 2.0 is a professional-grade super agent harness. Moving beyond the limitations of standalone agents, it functions as a comprehensive runtime infrastructure designed to orchestrate sub-agents, persistent memory, and isolated sandboxes. The system provides a “batteries-included” environment where agents transition from conversational interfaces to functional autonomous operators.
Version 2.0 vs. 1.x
Version 2.0 is a ground-up rewrite of the original framework. While the 1.x branch focused exclusively on “Deep Research” and remains available for community maintenance, all active development has shifted to the 2.0 harness architecture. This version introduces a generalized infrastructure capable of handling diverse workloads beyond research, including data pipelining, content automation, and software engineering.
Mission Statement
The project has evolved from a specialized research tool into a modular harness. The mission is to provide the foundational components—filesystem access, long-term memory, and hierarchical planning—required for agents to execute complex, multi-step tasks within a secure and extensible environment.
——————————————————————————–
2. Core Architecture and Framework Foundation
Technological Stack
The architecture is anchored by two primary frameworks:
- LangChain: Manages LLM interactions and chain logic.
- LangGraph: Chosen for its innovative approach to multi-agent orchestration. Unlike simple linear chains, LangGraph enables sophisticated state management and the execution of cyclical agent loops, allowing agents to refine results and recover from errors autonomously.
The Harness Model
The harness acts as a managed runtime for agent tenants. It abstracts the underlying complexities of tool execution and state persistence. A critical technical detail is the system’s normalization of context: DeerFlow normalizes plain-string model outputs and rich-content blocks into consistent JSON array responses via Pydantic validation. This ensures schema consistency and prevents provider-specific wrappers from dropping valuable suggestions or tool calls.
Context Engineering and Management
To maintain system integrity during long-duration sessions, DeerFlow employs dual-layer context management:
- Isolated Sub-Agent Context: Each sub-agent operates within a strictly scoped context. Isolation prevents “contextual pollution,” ensuring sub-agents focus on specific sub-tasks without being distracted by the lead agent’s broader session history.
- Summarization and Compression: The system aggressively manages the context window by summarizing completed tasks, offloading intermediate data to the filesystem, and compressing irrelevant tokens to stay within model limits without losing progress.
——————————————————————————–
3. Key Functional Features
Agent Skills and Tools
- Skills: Defined as structured capability modules in Markdown, skills encapsulate workflows and best practices. Built-in skills include Research, Report Generation, Slide Creation, Web Pages, and distinct modules for Image and Video Generation.
- Progressive Loading: Skills are loaded dynamically only when required by the task, minimizing the initial context footprint and maximizing efficiency for token-sensitive models.
InfoQuest Integration
DeerFlow features deep integration with InfoQuest, an intelligent search and crawling toolset developed by BytePlus. This provides the harness with high-fidelity web exploration capabilities superior to standard search APIs.
Sub-Agent Orchestration
The lead agent utilizes a fan-out/converge workflow. It decomposes high-level objectives into granular tasks, spawning parallel sub-agents to execute them. Results are then converged and synthesized by the lead agent into the final deliverable.
Sandbox and Filesystem
Each task is allocated a dedicated execution environment and filesystem view.
| Provider | Technical Implementation | Security Context |
| AioSandboxProvider | Containerized isolation (Docker/K8s). | Supports secure shell execution and resource-intensive operations. |
| LocalSandboxProvider | Host-based mapping to per-thread directories. | Warning: Host bash is disabled by default as it is not a secure boundary. Re-enable only for trusted local workflows. |
Long-Term Memory
DeerFlow builds a persistent profile of user preferences and knowledge. During updates, the system employs skip-logic to detect and bypass duplicate fact entries, preventing memory bloat and ensuring data relevance across months of interaction.
——————————————————————————–
4. Setup and Configuration Guide
One-Line Agent Setup
For developers using coding agents (Claude Code, Cursor, Codex), the following prompt automates the environment setup:
“Clone the DeerFlow repo, use Docker if available, and stop once you’ve run make config and identified which API keys I still need to provide.”
Initial Configuration
git clone [repository_url]make install-deps(Required for local development).make config(Generatesconfig.yamland.env).
Deployment Options
| Feature | Option 1: Docker (Recommended) | Option 2: Local Development |
| Prerequisites | Docker, Docker Compose | Python 3.10+, Dependencies |
| Primary Command | make docker-dev | make dev |
| Use Case | Production-like isolation. | Rapid iteration and debugging. |
| Security | Containerized sandboxing. | Direct host access (High Risk). |
Model Integration
Configure models in config.yaml using langchain_openai:ChatOpenAI.
- CLI Providers:
- Codex: Reads credentials from
~/.codex/auth.json. - Claude Code: Requires variables such as
CLAUDE_CODE_OAUTH_TOKENor path to~/.claude/.credentials.json. On macOS, export auth explicitly as DeerFlow does not auto-probe the Keychain.
- Codex: Reads credentials from
——————————————————————————–
5. Advanced Capabilities and Integrations
Embedded Python Client (DeerFlowClient)
For low-latency library usage, the DeerFlowClient allows developers to embed the harness directly into Python applications without HTTP overhead. It returns schemas validated against Pydantic models, ensuring parity with the Gateway API.
Claude Code Integration
The claude-to-deerflow skill enables terminal-based orchestration:
- Execution Modes:
flash(speed),standard(balanced),pro(planning), andultra(multi-agent fan-out). - Capabilities: Streaming responses, thread management, and direct file uploads for analysis.
IM Channel Support
DeerFlow supports asynchronous tasking via messaging platforms using long-polling or WebSockets.
| Channel | Transport | Difficulty | Setup Requirements |
| Telegram | Bot API | Easy | HTTP Token via @BotFather. |
| Slack | Socket Mode | Moderate | App-Level Token (xapp) + Bot Scopes. |
| Feishu/Lark | WebSocket | Moderate | App ID/Secret + Long Connection mode. |
Observability
Full LangSmith Tracing is supported for auditing agent logic and LLM costs. Set LANGSMITH_TRACING=true and LANGSMITH_API_KEY in the .env to enable detailed execution traces.
——————————————————————————–
6. Model Recommendations and Technical Requirements
Performance Criteria
Successful harness operation requires models meeting four specific benchmarks:
- Long Context (100k+): Essential for deep research and multi-sub-agent synthesis.
- Reasoning: Must handle adaptive planning and task decomposition.
- Multimodal: Required for processing images and generated video content.
- Tool-use: Precise function calling for structured filesystem and bash operations.
Recommended Models
- Doubao-Seed-2.0-Code: Recommended for superior tool-use and reasoning within the harness.
- DeepSeek v3.2: Excellent performance-to-latency ratio for sub-agent tasks.
- Kimi 2.5: Optimized for extremely long context tasks.
——————————————————————————–
7. Security Architecture and Risk Mitigation
Default Security Posture
By design, DeerFlow defaults to the 127.0.0.1 loopback interface. This is a core defense-in-depth strategy to prevent accidental exposure of the high-privilege agent to untrusted networks.
High-Privilege Risks
The harness can execute system commands and modify files. Exposure to untrusted networks without mitigation leads to:
- Unauthorized Invocation: Remote execution of high-risk operations by malicious scanners.
- Compliance Risks: Potential for the harness to be weaponized for lateral movement or data exfiltration.
Mandatory Security Measures (Non-Local Deployment)
Engineers deploying outside a local trusted environment must implement:
- IP Allowlisting: Restrict access via
iptablesor hardware firewalls. - Authentication Gateways: Deploy a reverse proxy (e.g., Nginx) with mandatory pre-authentication.
- Network Isolation: Utilize dedicated VLANs to isolate the harness from broader internal networks.
XSS Mitigation
To protect users from malicious artifacts, the Gateway forces specific MIME types to download as attachments rather than rendering inline. This applies to:
text/htmlapplication/xhtml+xmlimage/svg+xml
——————————————————————————–
8. Project Metadata and Governance
- Licensing: Open-sourced under the MIT License.
- Governance: Contribution guidelines are detailed in
CONTRIBUTING.md. Security and regression testing (including Docker sandbox detection) are integrated into CI. - Key Contributors: Authored by Daniel Walnut and Henry Li, leveraging the foundational work of the LangChain and LangGraph communities.